Wolfram Function Repository
Instant-use add-on functions for the Wolfram Language
Function Repository Resource:
Cryptographic hash-based message authentication code used to verify data integrity and authenticity
ResourceFunction["HMAC"][expr, key] calculates message authentication code for expr using secret key key and the SHA256 hash function. | |
ResourceFunction["HMAC"][expr, key, hash] calculates message authentication code for expr using secret key key and hash function hash. |
| expr | byte representation obtained by BinarySerialize |
| "string" | bytes in the UTF-8 representation of string |
| ByteArray[…] | literal bytes in the byte array |
| "MD2" | 128-bit MD2 code |
| "MD4" | 128-bit MD4 code |
| "MD5" | 128-bit MD5 code |
| "SHA" | 160-bit SHA-1 code |
| "SHA224" | 224-bit SHA code |
| "SHA256" | 256-bit SHA code (default) |
| "SHA384" | 384-bit SHA code |
| "SHA512" | 512-bit SHA code |
| "RIPEMD160" | 160-bit RIPEMD code |
| "RIPEMD160SHA256" | RIPEMD-160 following SHA-256 (as used in Bitcoin) |
| "SHA256SHA256" | double SHA-256 code (as used in Bitcoin) |
| "SHA3-224" | 224-bit SHA3 code |
| "SHA3-256" | 256-bit SHA3 code |
| "SHA3-384" | 384-bit SHA3 code |
| "SHA3-512" | 512-bit SHA3 code |
| "Keccak224" | 224-bit Keccak code |
| "Keccak256" | 256-bit Keccak code |
| "Keccak384" | 384-bit Keccak code |
| "Keccak512" | 512-bit Keccak code |
Compute message authentication code using the default SHA256 hash and a secret key:
| In[1]:= |
| Out[1]= | 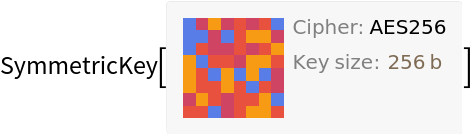 |
| In[2]:= |
| Out[2]= |
Compute a SHA3-based message authentication code:
| In[3]:= |
| In[4]:= |
| Out[12]= |
Compute HMAC using a password as a key:
| In[13]:= |
| Out[13]= |
Use a ByteArray key directly:
| In[14]:= |
| In[15]:= |
| Out[15]= |
For ByteArray or string message, literal bytes are used in HMAC computation:
| In[16]:= |
| In[17]:= |
| Out[17]= |
Use BaseEncode to convert byte array output to string encodings:
| In[18]:= |
| In[19]:= |
| Out[19]= |
| In[20]:= |
| Out[20]= |
This work is licensed under a Creative Commons Attribution 4.0 International License